Microsegmentation, Explained: A Comprehensive Guide
This article is part of our series on Zero Trust. For more information on Zero Trust, check out Zero Trust, Explained.
What is Segmentation?
Segmenting simply means dividing things into smaller groups. In business, we may talk about "customer segmentation" - a way of dividing customers into groups with similar behavior, often along demographic, geographic, or other lines. Done properly, this allows us to create more targeted messaging for each segment, making our marketing more powerful and effective.
Segmentation in cybersecurity is very similar, but with the goal of making control and visibility more powerful and effective. For example, network segmentation takes networks and divides them into smaller network that serve similar applications. Traffic passing between the segmented networks is forced through a specific point for traffic observation (e.g. threat detection) or application of security controls (e.g. firewalls).
Segmentation is an important tool in the cybersecurity toolbox. Some of the key benefits of segmentation include:
- Attack surface reduction - an attacker with access to one segment can't easily probe for vulnerabilities or launch attacks against machines or assets in another segment;
- Faster detection - the increased visibility in a segmented network increases the risk that attackers probing the network will trip an alarm;
- Attack containment - an attack, such as ransomware, that affects one segment can’t spread to the other; and
- Faster time-to-recovery - containment makes it much faster and easier to restore service by limiting the number of servers affected.
Segmentation is a powerful cybersecurity practice with many benefits. So what is “micro-segmentation,” and what has driven its popularity in the last few years?
Types of Segmentation
As it turns out, there are many ways to implement segmentation. Which one is “best” largely depends on the level of security required for what you're trying to protect.
No Segmentation
The most basic form of segmentation is the “flat network” – one with no segmentation at all. Many corporate networks have evolved as flat networks, because the network is viewed as a shared service for applications. A flat network is convenient to set up and manage, as granting network access is sufficient to provide access to all of the corporate applications and data.

"Flat" network: everything is connected
While this approach is certainly convenient from a network operations perspective, this type of security operations is extremely reactive. You can keep endpoints patched and antivirus rules updated, but once an active threat, such as an intruder or ransomware, is detected in your network, you're in a race against the clock to try to defend the network.
Physical Segmentation
At the opposite end of the spectrum, we have physical segmentation, where networks that are are not even connected to each other. This is often referred to as an “air-gap.” Since there is no network connection, threats such as ransomware will not be able to directly cross the air-gap – though, as was shown with Stuxnet, it’s still possible for a determined attacker to reach machines that are air-gapped through non-network means such as USB drives. However, such “Sneakernet” operations may be complex enough that they require the resources of a nation-state – as well as a bit of good luck – to plan and carry out.

Physical segmentation: the two networks are disconnected
For practical purposes, no communication exists between physically segmented networks. Depending on the criticality of the application, that can be highly desirable.
Network Segmentation
Network Segmentation uses network infrastructure to create a logical, rather than physical, gap between networks. Examples of network segmentation tools include firewalls, which are used to block traffic based on certain policies at the network perimeter, or switch ACLs, which filter traffic matching certain rules.
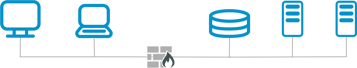
Network Segmentation: networks are logically separated by the firewall
As it depends on infrastructure, network segmentation is by definition coarse-grained; there are a relatively small number of insertion points for security policy enforcement. Even with advanced VLANs and VXLANs, creating network segmentation with infrastructure is complex, tedious, and error-prone, and disruptive to applications.
Since the segments are still relatively large, the above benefits of segmentation are also limited. As a result, many organizations have not bothered to segment their networks, and still use flat networks.
If valid business applications need to communicate between segments, standard IT practice is to create a "hole" in the firewall to allow that traffic. Organizations that have implemented network segmentation have reported that over time, the accumulation of holes leads to significantly degraded segmentation effectiveness.
Micro-segmentation
Network segmentation has existed for decades and is commonly recommended in CVE advisories. Yet organizations still routinely fall victim to ransomware, APTs, and other attacks. The reality is that the low benefit from coarse segmentation, coupled with the time and effort needed to rearchitect the network makes traditional network segmentation undesirable. Organizations would rather do almost anything else - including clean up a ransomware attack - before they rearchitect the network!
Micro-segmentation attempts to address both of these problems. It adds security policy enforcement in front of each workload, dramatically hampering the propagation of malware and other attacks and delivering the maximum security benefit.
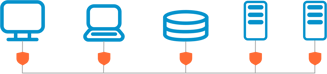
Micro-segmentation: each workload is individually protected
It also automates the difficult and tedious process of managing fine-grained security policies to make micro-segmentation practicable.
How this is done is solution-dependent. Some vendors take over direct responsibility for programming switch ACLs and firewall rules. This has the benefit of not requiring a software agent, but yielding control of these functions can significantly affect customers' operational practices. Such approaches must also be tested thoroughly in every environment in which they will be used.
Other vendors use a software agent to implement segmentation. Between these, the agent approach is preferred: it scales well, and is independent of the network implementation.
Another agentless method of implementing micro-segmentation is through a gatekeeper appliance, enforcing security policies in the network, but right at the edge of the workload.
Micro-segmentation is often discussed in directional terms ("north-south" and "east-west"). Typically, north-south refers to remote access, while east-west refers to lateral network access.
Micro-segmentation vs Software-Defined Perimeters for Zero Trust
At its beginning, micro-segmentation was envisioned as a tool for datacenter administrators, who needed a way to manage datacenter traffic without needing to know what applications were running.
As a result, many early micro-segmentation solutions are intended for deployment at scale - once deployed pervasively, the tool would visualize traffic flows and suggest rules to specifically allow traffic between source and destination servers.
This problem statement is different from the Zero Trust model. In a Zero Trust Architecture such as NIST SP800-207, an administrator needs to define the Implicit Trust Zone, typically with a new perimeter that blocks any network accesses that do not go through the Policy Enforcement Point.
In contrast to the datacenter case, where the admin does not understand what applications are running, when implementing a Zero Trust Architecture, the admin typically knows exactly what the resource being protected is. The resource may comprise thousands of machines or servers - but could also be a single server.
Software-Defined Perimeters (SDP) are similar to micro-segmentation solutions, and may leverage many of the same deployment models, but have been specifically tailored to be simple and cost-effective for implementing a Zero Trust Architecture.
Another relevant point differentiating micro-segmentation from Software-Defined Perimeters is what secure policies you are able to enforce. For example, putting an intrusion detection system (IDS) in front of every workload would be considered micro-segmentation. It would not be capable of creating the NIST 800-207 Implicit Trust Zone.

Micro-segmentation with the wrong security isn't Zero Trust
For a detailed overview of the broader Zero Trust movement and its benefits, check out our resource, Zero Trust, Explained.
Zentera’s CoIP Platform combines both micro-segmentation and Zero Trust Network Access (ZTNA) capabilities. This enables organizations to take advantage of features such as Application Chambers and Application Networks to reduce their attack surface, while maintaining operational flexibility.
|
Who Can Benefit from Micro-segmentation?
Micro-segmentation solutions are targeted for large datacenters. Their feature set, workflow, and business models are aligned with large deployments.
But nearly every organization has critical assets and data that, should they be lost due to a cyber attack, would significantly threaten business continuity – even small businesses have databases of client information. These days, a cyber attack is no longer a question of “if” - it’s “when.” These companies should look for SDP solutions which can help implement a NIST 800-207 Zero Trust Architecture.