Release 6.5.1 - Zero Trust Meets Analytics

by Mike Ichiriu
February 22, 2021
Release 6.5.1 is out, packing new features to support managing Zero Trust projects for IT and OT environments! The team has been hard at work putting the finishing touches on these new capabilities, and we are excited to share them with you.
Here's some of what's new:
- Zero Trust analytics and XDR Intelligence
 CoIP Access Platform now reports scores that represent the attack surface that's presented by onboarded applications/servers. Administrators now get instant feedback on how policy changes they implement affect the attack surface. As administrators progressively step up the security level of an application, they to evaluate and communicate the relative impact of the policy changes, as well as quickly identify and prioritize which applications need more help.
CoIP Access Platform now reports scores that represent the attack surface that's presented by onboarded applications/servers. Administrators now get instant feedback on how policy changes they implement affect the attack surface. As administrators progressively step up the security level of an application, they to evaluate and communicate the relative impact of the policy changes, as well as quickly identify and prioritize which applications need more help.
These data are combined into the full policy information and event logs as part of CoIP XDRi, for full end-to-end visibility of a complex, hybrid environment. - New policy recommendations engine
 Together with the new scoring system, we've introduced a policy recommendations engine that suggests actions for an administrator to consider. Examples of actions may include closing ports, blocking lateral communications between servers in the same application tier, or applying advanced filtering features such as Application Interlock. The recommendations engine also shows the potential improvement, helping administrators to prioritize actions based on the impact and value to segmentation and attack surface reduction.
Together with the new scoring system, we've introduced a policy recommendations engine that suggests actions for an administrator to consider. Examples of actions may include closing ports, blocking lateral communications between servers in the same application tier, or applying advanced filtering features such as Application Interlock. The recommendations engine also shows the potential improvement, helping administrators to prioritize actions based on the impact and value to segmentation and attack surface reduction. - New policy dashboards
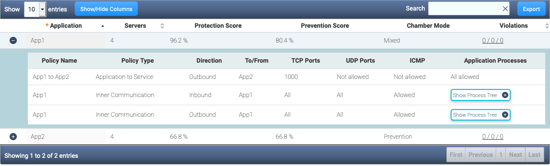 In 6.5.1, we've created new policy dashboards that quickly present end-to-end policies in a simple way, making it easier for admins to review policies across all applications over the entire deployment.
In 6.5.1, we've created new policy dashboards that quickly present end-to-end policies in a simple way, making it easier for admins to review policies across all applications over the entire deployment. - Support for managing Micro-segmentation Gatekeeper appliances

The Micro-Segmentation Gatekeeper (MSG) line, first introduced in Q4 2020, makes agentless onboarding for critical servers and devices, and enables full east-west micro-segmentation controls. With release 6.5.1, the MSG is now a full member of the CoIP family, and can be managed through the zCenter CoIP Controller. Tasks from securing a critical IT server to providing secure remote access to an IIoT machine become easier with orchestration. Admins can also update threat detection rules or create their own, and instantly provision them to all MSGs under management.
Upgrade packages for release 6.5.1 are now available on our support site; release 6.5.1 is also available on the AWS Marketplace with a limited trial license. To learn more, contact Zentera Sales.




