Water OT Cybersecurity in 2026: Regulations, Threats, and a Practical Path Forward
Water utilities have operated on voluntary cybersecurity guidance for years. That era just ended.
The Rules Just Changed
 On March 11, 2026, New York adopted the first mandatory cybersecurity regulations for drinking water and wastewater facilities in the United States. The rules require utilities to separate operational technology from IT networks and the internet, enforce multi-factor authentication, eliminate default credentials, report cyber incidents under strict mandatory timelines, and implement continuous network monitoring at larger facilities. Compliance deadlines extend through the end of 2027.
On March 11, 2026, New York adopted the first mandatory cybersecurity regulations for drinking water and wastewater facilities in the United States. The rules require utilities to separate operational technology from IT networks and the internet, enforce multi-factor authentication, eliminate default credentials, report cyber incidents under strict mandatory timelines, and implement continuous network monitoring at larger facilities. Compliance deadlines extend through the end of 2027.
New York went first, but EPA's national cybersecurity guidance already aligns with the same controls. Other states are watching this closely as a model for their own rulemaking. Systems serving more than 3,300 people are due to recertify their risk and resilience assessments under the America's Water Infrastructure Act, with cybersecurity now an explicit component, and many are scrambling to complete them. At the federal level, CIRCIA will require critical infrastructure operators, including water utilities, to report cyber incidents within 72 hours once the final rule takes effect.
These regulations demand more than monitoring your network. They require active enforcement: physical separation of OT from IT, access control at every boundary, and the ability to contain an incident before it spreads.
The Threat Is Already Inside the Sector
The urgency behind these mandates comes from real incidents, not hypothetical scenarios.
In Littleton, Massachusetts, Chinese state-backed actors linked to the Volt Typhoon campaign spent nearly a year inside a small municipal water and electric utility's network. They entered through an unpatched FortiGate firewall and moved laterally through file servers, a domain controller, and a VMware vCenter server that sat adjacent to OT assets. They exfiltrated operating procedures and spatial layout data, collecting intelligence that could support disruption of OT operations in a future geopolitical crisis. The utility only discovered the compromise when the FBI called.
What would have changed the outcome? Segmentation at the IT/OT boundary would have blocked the lateral movement from vCenter to OT-adjacent systems, removing the access path that gave Volt Typhoon the option to disrupt operations if a crisis warranted it. That lateral movement, from IT into OT-adjacent infrastructure, is the step that made this a critical infrastructure incident rather than an IT breach.
In Aliquippa, Pennsylvania, Iranian-linked actors from the CyberAv3ngers group accessed a Unitronics PLC at a remote pumping station. The device had a default password and its HMI was exposed to the internet. They walked right in. EPA subsequently identified similar exposures at hundreds of water systems using basic assessments that any utility can request at no cost from CISA.
What would have changed the outcome? Two fundamentals: changing the default password and removing the HMI from the public internet. No advanced technology required.
These were not sophisticated attacks. They exploited basic gaps (flat networks, default credentials, internet-exposed controllers) that exist at thousands of water utilities running legacy SCADA and PLCs over unsegmented Modbus/TCP and serial Modbus RTU infrastructure with no dedicated OT security staff.
What Compliance Actually Demands
The specific frameworks vary, but every one of them (CISA's Cybersecurity Performance Goals, AWWA's 12 Fundamentals, NIST CSF 2.0, New York's new regulations, and your own state's emerging requirements) converges on the same core OT controls:
Separate OT from IT and the internet. This is the number-one requirement across every framework and the foundation that makes everything else work.
Enforce MFA and eliminate default or shared credentials. Especially for remote access and third-party vendor connections into OT environments.
Monitor and log OT network activity. Know what devices are communicating, with what, and when, so you can detect anomalies and respond.
Build and test an incident response plan. Include documented manual operations procedures so your plant can keep running if automated systems are compromised.
These are not four separate projects. They build on each other, and the first steps are free.
Why This Is Harder Than It Sounds
Knowing what controls to implement and being able to implement them are two different things in water OT.
 The typical water district runs PLCs and RTUs with 15- to 25-year lifecycles. A decades-old Allen-Bradley SLC 500 or CompactLogix at a remote pump station cannot run a security agent, cannot support modern authentication, and cannot be firmware-updated without a multi-month change control process. Ripping it out means a capital project, not a security project.
The typical water district runs PLCs and RTUs with 15- to 25-year lifecycles. A decades-old Allen-Bradley SLC 500 or CompactLogix at a remote pump station cannot run a security agent, cannot support modern authentication, and cannot be firmware-updated without a multi-month change control process. Ripping it out means a capital project, not a security project.
Networks grew organically over decades on flat Layer 2 architectures. Introducing segmentation means untangling undocumented dependencies. Insert a firewall rule in the wrong place and you block the Modbus traffic between your SCADA server and your chlorine dosing system at 2am. In water, mis-segmentation is not an IT inconvenience. It is a potential public health violation. If chlorine residual drops below minimum because a control link was severed, the utility is in violation of its discharge permit and the state health department gets a call.
Water treatment operates 24/7/365. Unlike manufacturing, there is no annual shutdown window for security retrofits. Every change must be incremental, fail-safe, and reversible. And in the public sector, even funded projects face procurement and approval cycles that can add three to six months before a deployment begins.
Staffing is the binding constraint. A Microsoft and Cyber Readiness Institute pilot released in March 2026 found that only about 38 percent of participating water utilities completed a basic cyber readiness program, not because they lacked interest, but because they lacked the staff and hands-on support to follow through. Many districts have a single IT person managing security alongside billing, phones, and the public website. Staff turnover compounds the problem. The person who starts a cyber program may not be the person who finishes it, and institutional knowledge walks out the door with them.
The reality is that CISOs and IT managers at small water districts are being asked to solve a problem that Fortune 500 companies struggle with, on a fraction of the budget, with a fraction of the staff, and with infrastructure that predates the internet. The problem is not that water utilities do not know they need to act. It is that the available approaches were not designed for their constraints.
Where to Start: A Practical Roadmap
The most impactful steps are also the cheapest. EPA, CISA, and AWWA have built a stack of free resources specifically for water utilities. Start there before evaluating any vendor product.
Step 1: Use the free resources that already exist
Get a free CISA vulnerability assessment. CISA offers no-cost vulnerability scans and on-site cybersecurity assessments to community water systems of any size. These use a checklist derived from CISA's Cybersecurity Performance Goals and produce a summary report with a prioritized risk management plan. There is no catch and no vendor obligation. If you do one thing after reading this blog, request an assessment.
Download EPA's incident response templates. EPA released an updated Cybersecurity Incident Response Plan template in October 2025 specifically designed for water and wastewater utilities. It includes incident-specific checklists and a procurement checklist for evaluating vendor security. These are free, they are tested, and they satisfy the incident response planning requirement in every framework.
Join WaterISAC. Membership is free for water and wastewater utilities. WaterISAC provides sector-specific threat intelligence and alerts, including the advisories that warned about CyberAv3ngers targeting Unitronics PLCs before the Aliquippa incident. If you are not a member, you are missing early warning signals tailored to your sector.
Use AWWA's cybersecurity self-assessment tool. AWWA's guidance and assessment tool is recognized by EPA, CISA, and NIST. It maps directly to the NIST Cybersecurity Framework and to AWIA Section 2013 requirements. It will show you where your gaps are in a structured way, using language your board and your regulators understand.
Step 2: Fix the basics that stop real attacks
The Aliquippa incident was not stopped by a sophisticated security platform. It was made possible by a default password on an internet-exposed device. Before investing in any technology, address these fundamentals:
Change every default credential on every OT device. This includes PLCs, HMIs, RTUs, and network switches. CISA's CPG 1.A is explicit: default passwords are the number-one exploitable weakness. Document the changes and store credentials securely.
Remove every OT device from the public internet. If an HMI or PLC management interface is reachable from the internet, take it offline or put it behind a VPN immediately. This is the single highest-impact change you can make. EPA found this exposure at hundreds of systems during routine checks.
Enable MFA on all remote access. If your operators or vendors connect to OT systems remotely, require multi-factor authentication. If your current remote access solution does not support MFA, that is a procurement priority.
Document your OT asset inventory and network topology. You cannot protect what you do not know exists. Walk your plants and pump stations. Identify every device on the network, what it talks to, and over what protocol. This inventory becomes the foundation for every subsequent step, and it is a requirement under AWIA.
These are not optional prerequisites to get out of the way. For most water districts, these four actions will reduce more risk than any product purchase. They address the exact attack vectors used in Aliquippa and in the Iranian and Russian campaigns targeting water utilities through 2024 and 2025.
Step 3: Tackle the harder architectural controls
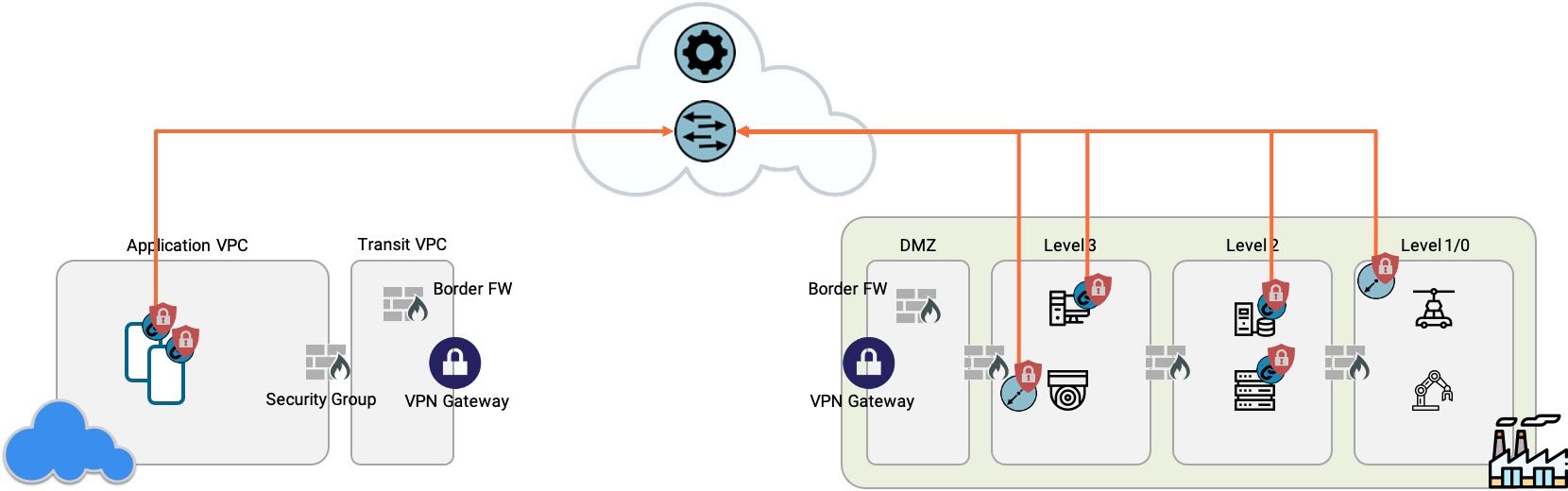
Once the basics are in place, the next challenge is the one that the regulations were written to solve: separating OT from IT at the network level, segmenting critical zones from each other, and controlling who and what can access each zone.
This is where it gets genuinely difficult, especially for districts running flat legacy networks where segmentation has never existed. Here is what the challenge looks like and what the options are.
Understanding zones and conduits. IEC 62443, the international standard for industrial cybersecurity architecture, provides the blueprint that underpins what every framework is asking you to do. The core concept is dividing your OT environment into security zones (groups of assets with similar criticality and trust levels) and controlling all traffic between zones through managed conduits. Your SCADA server, your chemical dosing PLCs, and your remote pump stations should not be in one flat zone where any device can reach any other device.
The segmentation approaches available to you each have strengths and real limitations. None is a silver bullet. Here they are with equal honesty about what each can and cannot do.
VLAN-based segmentation uses your existing managed switches to create separate network segments with access control lists governing traffic between them.
- Best for: Creating the primary boundary between IT and OT networks. This is the most common and most proven starting point for water utilities. Most managed switches already support VLANs, so you may not need to purchase new hardware for the initial IT/OT split.
- What it cannot do: VLANs provide limited granularity within the OT network itself. Segmenting individual PLCs or creating micro-zones within a plant typically requires additional technology.
- What can go wrong: Requires careful documentation of existing traffic flows before implementation. Undocumented Modbus or OPC dependencies between devices can be accidentally severed, potentially disrupting chemical dosing or other safety-critical processes. Changes to switch configurations on a live plant network carry real operational risk. Test in a maintenance window and maintain rollback procedures.
Firewall-based segmentation places dedicated firewall appliances at key network boundaries. Purpose-built OT firewalls from vendors like Fortinet, Palo Alto, and Cisco can inspect industrial protocols and enforce rules at the protocol level.
- Best for: Enforcing policy at the IT/OT boundary and between major OT zones where protocol-level inspection adds value. Well-established technology with broad vendor support and extensive deployment history in critical infrastructure.
- What it cannot do: Firewalls are perimeter devices. They protect zone boundaries but do not provide granular micro-segmentation within a zone. They also require ongoing rule management as your network evolves.
- What can go wrong: A firewall is an inline device on your control network. If it fails, traffic stops unless you have configured bypass or redundancy. Rule misconfiguration carries the same public health risk as VLAN misconfiguration: a blocked Modbus flow to a chlorine dosing system is a blocked Modbus flow regardless of what blocked it. Firewalls add latency, which matters for time-sensitive control loops. Budget for ongoing rule management and periodic review.
Overlay-based microsegmentation deploys a software-defined network layer that creates logical security zones on top of your existing physical network. Some implementations use inline gateway appliances to enforce access control on legacy devices that cannot run software agents.
- Best for: Segmenting legacy devices that cannot support agents or modern authentication, and creating granular micro-zones without re-architecting the physical network.
- What it cannot do: An overlay does not replace the need for basic network hygiene (credential management, internet exposure remediation) or for asset visibility. It is an enforcement layer, not a complete security program.
- What can go wrong: An overlay gateway is an inline device on your control network, carrying the same failure and misconfiguration risks as a firewall. If the gateway fails or a policy is wrong, control traffic can be disrupted. Hardware bypass mitigates device failure but does not protect against policy errors. This is a newer approach with fewer water-sector reference deployments than VLANs or firewalls. Always deploy in observation mode first and validate thoroughly before enforcing on any safety-critical control loop.
Visibility-first platforms from vendors like Dragos, Claroty, and Nozomi Networks passively discover assets, map communication flows, monitor traffic, and detect anomalies on your OT network.
- Best for: Understanding what is on your network before you segment anything. Particularly valuable for districts that have never inventoried their OT assets or mapped device-to-device communication. Non-intrusive: passive monitoring does not change traffic flows or risk disrupting operations.
- What it cannot do: Visibility does not enforce access control or prevent lateral movement. It detects threats and anomalies but does not block them. A visibility platform will show you that an attacker moved from vCenter to your SCADA server. It will not stop that movement.
- What can go wrong: The primary risk is a false sense of security. Deploying a visibility platform and stopping there leaves you without the enforcement controls that current regulations require. Visibility is a necessary foundation, not a complete solution. Budget for the enforcement step that follows.
Most districts will use a combination of these approaches: visibility to understand the environment, VLANs or firewalls for major zone boundaries, and potentially overlay microsegmentation for specific legacy devices or remote sites that are difficult to protect any other way. The right mix depends on your network complexity, staff capacity, budget, and risk tolerance.
What matters more than the technology is the approach. Start with the highest-consequence assets. In water, that means chemical dosing controls, disinfection systems, SCADA master stations, and any remote site with internet or cellular connectivity. Segment those first. Test every change with documented rollback procedures. Expand incrementally. Accept that full segmentation is a multi-year journey, not a single project.
Step 4: Apply for funding
Cybersecurity funding for water utilities has expanded significantly. Do not assume you cannot afford to act.
New York SECURE grants provide up to $50,000 for cybersecurity assessments and $100,000 for upgrades including segmentation, monitoring, and incident response planning. Applications are due May 15, 2026.
EPA's State Revolving Fund and WIFIA programs accept cybersecurity projects when bundled into infrastructure loan applications, filed through your state's administering agency (in California, for example, that is the State Water Resources Control Board). These are subsidized loans, not grants, but the rates are favorable and the cyber eligibility is relatively new.
CISA's State and Local Cybersecurity Grant Program provides funding that states can direct toward water utility cybersecurity improvements. Check with your state's homeland security agency for allocation details.
Free vendor programs for qualifying utilities. Several OT security vendors offer free or community-tier access to their platforms for small and mid-size water utilities. The Dragos Community Defense Program provides free OT visibility platform licenses to U.S.-based water, electric, and gas utilities with under $100 million in annual revenue. Claroty offers programs for state, local, and education (SLED) customers. Nozomi Networks provides community editions and trial access. If you qualify for any of these, they are a no-cost path to foundational OT visibility.
Step 5: Sustain and prove compliance
Cybersecurity is not a project with an end date. Build a sustainable rhythm.
Conduct quarterly reviews of your asset inventory, access policies, and zone configurations. Test your incident response plan at least annually through a tabletop exercise (EPA's Tabletop Exercise Tool is designed for this). Maintain an audit trail that documents what controls you have implemented, when, and why. This evidence package is what regulators and auditors will ask for under AWIA, under state regulations, and under CIRCIA when finalized.
And when staff turn over, and they will, make sure the documentation is clear enough that the next person can understand and maintain what you built.
The Bottom Line
Water cybersecurity has shifted from voluntary guidance to enforceable mandates. New York set the precedent. Federal requirements are coming. Nation-state actors are already pre-positioned inside the sector.
The path forward is not buying a single product. It is a layered progression: free assessments and basic hygiene first, architectural improvements second, sustained compliance third. The free resources from EPA, CISA, AWWA, and WaterISAC exist specifically for districts that are resource-constrained. Use them.
For districts that have completed the fundamentals and are evaluating network segmentation architectures, whether VLAN-based, firewall-based, or overlay-based, the critical factors are fail-safe design (your plant cannot stop treating water because a security device failed), compatibility with legacy equipment (your 20-year-old PLCs are not going away), and incremental deployability (every change must be reversible and testable without downtime). Evaluate vendors against those criteria, not against marketing claims.
Start with what matters most. Expand as budget and staffing allow. The attacks that succeeded in this sector were not sophisticated. The controls that would have stopped them are not expensive. The gap is execution, and closing it starts with the next step you take.
Frequently Asked Questions
- What are New York's new water cybersecurity regulations?
Adopted March 11, 2026, New York's rules require water and wastewater facilities to separate OT from IT networks, enforce multi-factor authentication, report cyber incidents under strict mandatory timelines, conduct risk assessments, and implement network monitoring for larger facilities. Compliance deadlines extend through the end of 2027. These are the first state-level mandatory cybersecurity regulations for water utilities in the United States. - How can water utilities protect legacy SCADA and PLC systems?
Start with the basics: change default credentials, remove devices from the public internet, and enable MFA on all remote access. For devices that cannot run modern security software, the most common options are isolating them on dedicated network segments using VLANs, placing them behind OT firewalls with protocol-aware rules, or deploying overlay-based gateways that enforce access control at the network boundary without modifying the device. Each approach carries tradeoffs in complexity, operational risk, and cost. The right choice depends on the device, the network, and the district's risk tolerance. - What is the difference between OT visibility and OT protection for water districts?
OT visibility platforms discover assets on your network and detect anomalous behavior. They tell you what is happening but do not block it. OT protection adds active enforcement through network segmentation, access control, and encryption that prevents unauthorized access and contains lateral movement. Current regulations increasingly require both capabilities. Many districts start with visibility because it is non-intrusive, then add enforcement controls as their program matures. - What free cybersecurity resources are available to water utilities?
CISA offers free vulnerability scans and no-cost cybersecurity assessments to community water systems of any size. EPA provides incident response plan templates, cybersecurity checklists, and a tabletop exercise tool. AWWA's cybersecurity self-assessment tool maps to NIST CSF and AWIA requirements. WaterISAC membership is free for water and wastewater utilities and provides sector-specific threat intelligence. Several vendors also offer free or community programs for qualifying utilities, including the Dragos Community Defense Program, Claroty's SLED program, and Nozomi Networks community access. - How does IEC 62443 apply to water utilities?
IEC 62443 is the international standard for industrial cybersecurity architecture. Its zones-and-conduits model provides the engineering blueprint for segmenting OT networks by criticality and controlling traffic between zones, which is the same approach that New York's regulations, CISA's guidance, and AWWA's fundamentals all require. While not currently mandated for water utilities by U.S. regulations, it provides the most rigorous technical framework for planning and evaluating OT segmentation architectures.

Written by Mike Ichiriu
Mike Ichiriu is VP of Marketing and Product at Zentera Systems, where he leads product strategy for the company, including its Zero Trust and agentic AI security initiatives.
A Certified Cloud Security Professional (CCSP) and frequent speaker on enterprise security, Mike has 25+ years of experience across cybersecurity, networking silicon, and enterprise software, and holds 15 U.S. patents.