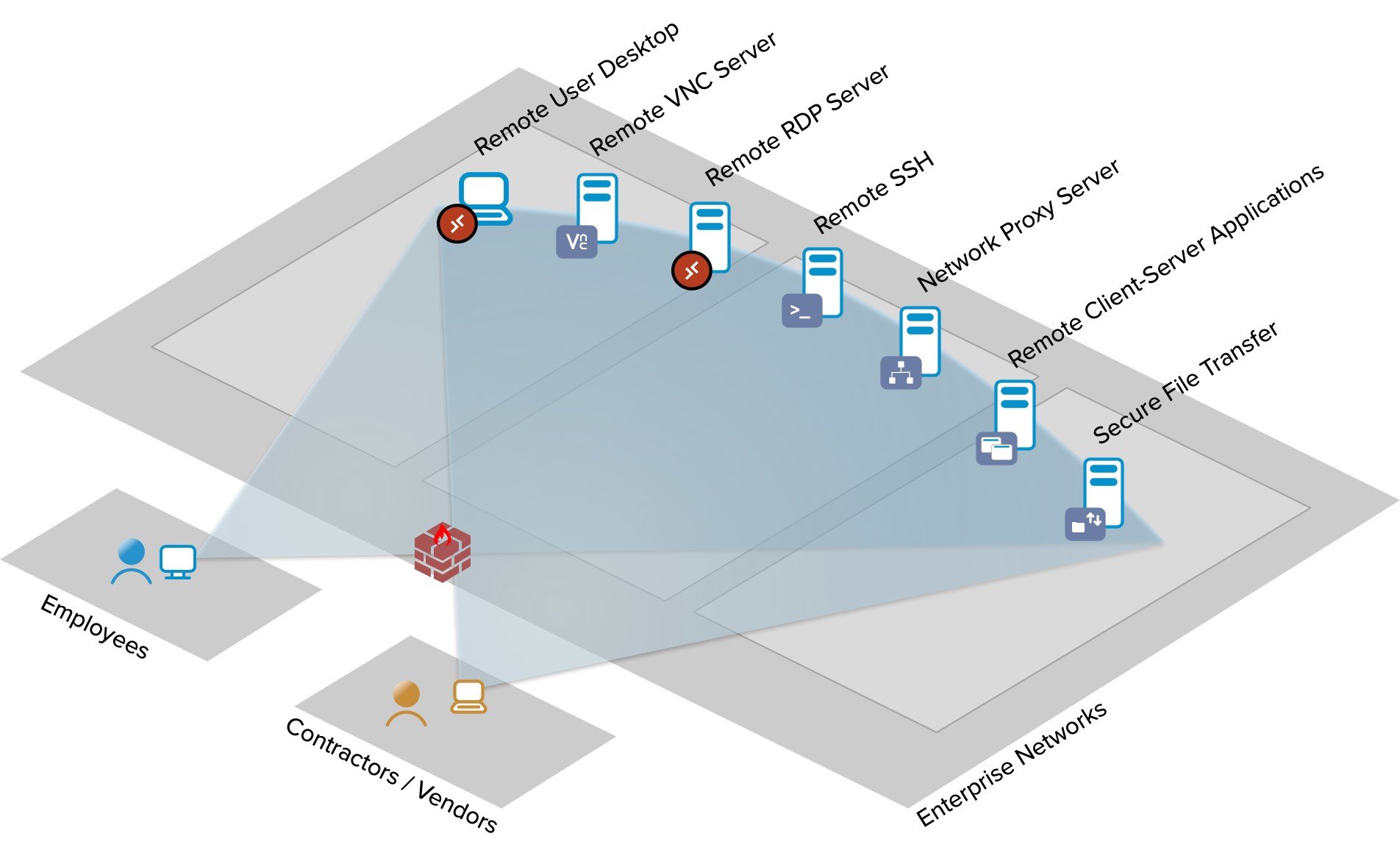
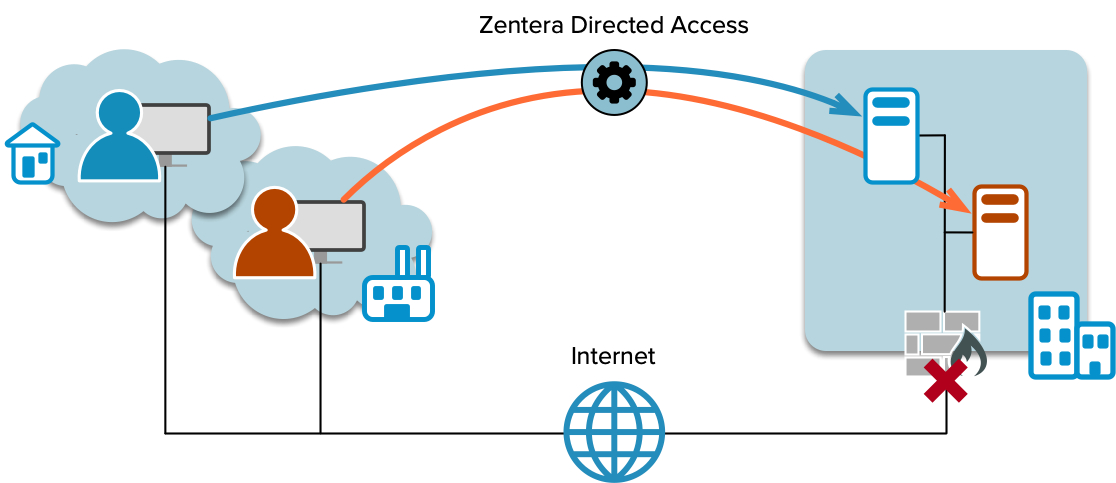
Secure Remote Access without Infrastructure
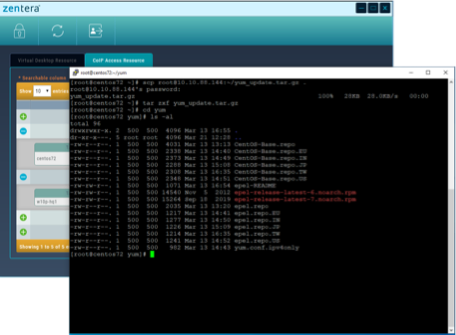
Expanded remote access increases cybersecurity risks. Not all remote access solutions are built to meet the security requirements or complexities of the modern corporate IT environment. Read how Zentera Secure Access builds on the principles of Zero Trust.